- Uncategorized
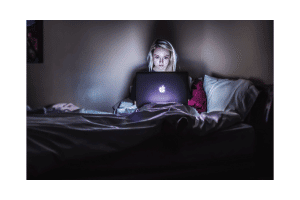
According to the 2023 FBI’s Internet Crimes Complaint Center (IC3), this past year, victims claim to have lost approximately $735 million to romance scammers. While romance scams are not something new, the popularity of online dating has allowed criminals to increase their pool of victims from the comfort of a computer screen. This Valentine’s Day, […]